A cybersecurity researcher is urging customers to improve Adobe Acrobat Reader after a repair was launched yesterday for a distant code execution zero-day with a public in-the-wild proof-of-concept exploit.
The flaw is tracked as CVE-2024-41869 and is a vital use after free vulnerability that might result in distant code execution when opening a specifically crafted PDF doc.
A “use after free” bug is when a program tries to entry information in a reminiscence location that has already been freed or launched. This causes surprising habits, reminiscent of a program crashing or freezing.
Nevertheless, if a risk actor is ready to retailer malicious code in that reminiscence location, and this system subsequently accesses it, it could possibly be used to execute malicious code on the focused gadget.
The flaw has now been fastened within the newest Acrobat Reader and Adobe Acrobat variations.
PoC exploit found in June
The Acrobat Reader zero-day was found in June by way of EXPMON, a sandbox-based platform created by cybersecurity researcher Haifei Li to detect superior exploits reminiscent of zero-days or hard-to-detect (unknown) exploits.
“I created EXPMON as a result of I seen that there have been no sandbox-based detection and evaluation techniques particularly specializing in detecting threats from an exploit or vulnerability perspective,” Li instructed BleepingComputer.
“All the opposite techniques do detection from a malware perspective. The exploit/vulnerability perspective is way wanted if you wish to go extra superior (or, early) detection.”
“For instance, if no malware is dropped or executed resulting from sure circumstances, or if the assault doesn’t use any malware in any respect, these techniques would miss such threats. Exploits function fairly otherwise from malware, so a unique strategy is required to detect them.”
The zero-day was found after numerous samples from a public supply have been submitted to EXPMON for evaluation. These samples included a PDF containing a proof-of-concept exploit that triggered a crash.
Whereas the PoC exploit is a piece in progress and accommodates no malicious payloads, it was confirmed to use a “person after free” bug, which could possibly be used for distant code execution.
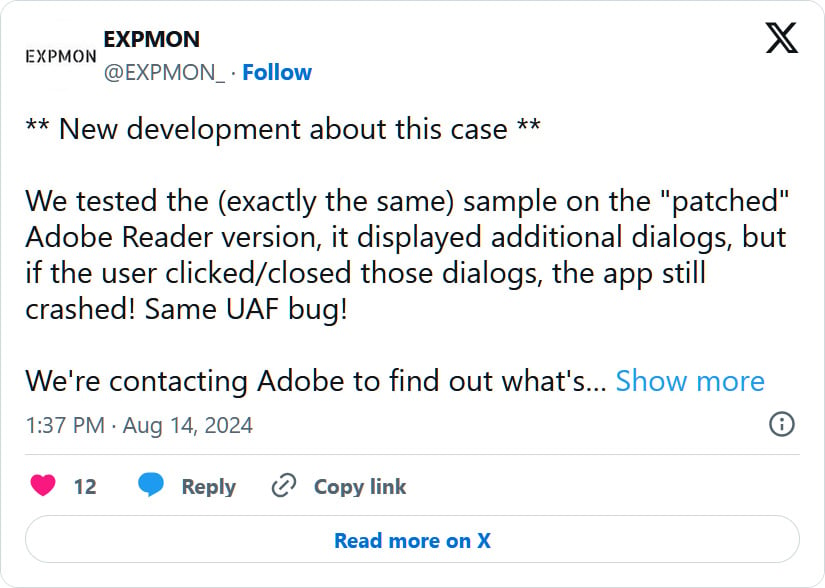
After Li disclosed the flaw to Adobe, a safety replace was launched in August. Nevertheless, the replace didn’t repair the flaw and will nonetheless be triggered after closing varied dialogs.
“We examined the (precisely the identical) pattern on the “patched” Adobe Reader model, it displayed extra dialogs, but when the person clicked/closed these dialogs, the app nonetheless crashed! Similar UAF bug!,” tweeted the EXPMON X account.
Yesterday, Adobe launched a new safety replace that fixes the bug, now tracked as CVE-2024-41869.
Li will likely be releasing particulars on how the bug was detected on EXPMON’s weblog and additional technical data in an upcoming Test Level Analysis report.