If you happen to’re in control of cybersecurity for a United States authorities company, you’re already accustomed to Memorandum M-22-09, “Shifting the U.S. Authorities Towards Zero Belief Cybersecurity Rules,” which the US Workplace of Administration and Price range issued in January 2022. This memo set a September 30, 2024, deadline for assembly “particular cybersecurity requirements and targets” towards implementing a Zero Belief structure in compliance with the Govt Order on Bettering the Nation’s Cybersecurity.
Microsoft has embraced Zero Belief rules, each in our safety merchandise and in the way in which we safe our personal enterprise atmosphere. We’ve been serving to 1000’s of organizations worldwide transition to a Zero Belief safety mannequin, together with navy departments and civilian companies. Over the previous three years, we’ve listened to our US authorities prospects, so we will construct wealthy new security measures that assist them meet the necessities described within the Govt Order, after which assist their deployments. These developments embrace certificate-based authentication within the cloud, Conditional Entry authentication energy, cross-tenant entry settings, FIDO2 provisioning APIs, Azure Digital Desktop assist for passwordless authentication, and device-bound passkeys.
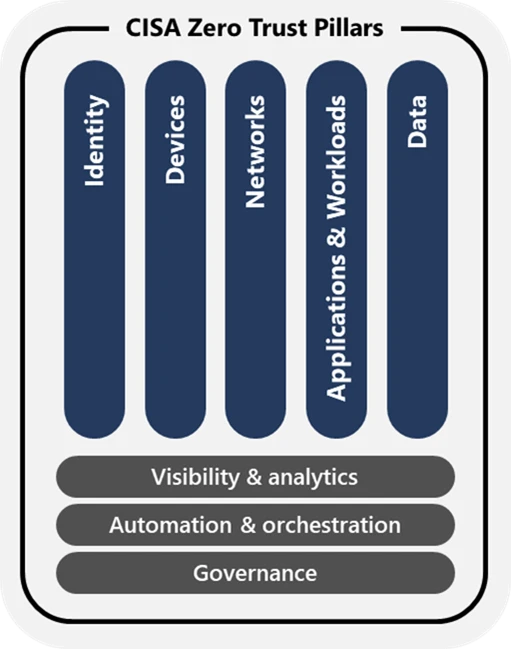
The illustration beneath depicts the Zero Belief Maturity Mannequin Pillars adopted by the US Cybersecurity and Infrastructure Safety Company (CISA).
Because the memo’s deadline approaches, we’d wish to rejoice the progress our prospects have made utilizing the capabilities in Microsoft Entra ID not solely to satisfy necessities for the Identification pillar, but in addition to cut back complexity and to enhance the person expertise for his or her workers and companions.
Microsoft Entra ID helps US authorities prospects meet the M-22-09 necessities for identification
US authorities companies are adopting Microsoft Entra ID to consolidate siloed identification options, cut back operational complexity, and enhance management and visibility throughout all their customers, because the memo requires. With Microsoft Entra ID, companies can implement multifactor authentication on the utility stage for extra granular management. They will additionally strengthen safety by enabling phishing-resistant authentication for employees, contractors, and companions, and by evaluating system data earlier than authorizing entry to assets.
Imaginative and prescient:
Company employees use enterprise-managed identities to entry the functions they use of their work. Phishing-resistant multifactor authentication protects these personnel from subtle on-line assaults.
Actions:
- Companies should make use of centralized identification administration techniques for company customers that may be built-in into functions and customary platforms.
- Companies should use robust multifactor authentication all through their enterprise.
- Multifactor authentication have to be enforced on the utility layer, as a substitute of the community layer.
- For company employees, contractors, and companions, phishing-resistant multifactor authentication is required.
- For public customers, phishing-resistant multifactor authentication have to be an possibility.
- Password insurance policies should not require use of particular characters or common rotation.
- When authorizing customers to entry assets, companies should take into account a minimum of one device-level sign alongside identification details about the authenticated person.
Supply: M-22-09: Shifting the US Authorities Towards Zero Belief Cybersecurity Rules, issued by the US Workplace of Administration and Price range, January 2022, web page 5.
Lots of our US authorities civilian and navy prospects wish to use the identical options throughout their totally different environments. Because it’s obtainable in secret and top-secret Microsoft Azure Authorities clouds, companies can standardize on Microsoft Entra ID to safe person identities, to configure granular entry permissions in a single place, and to supply easier, simpler, and safer sign-in experiences to functions their workers use of their work.
Microsoft Entra ID
Set up Zero Belief entry controls, forestall identification assaults, and handle entry to assets.

Utilizing Microsoft Entra ID as a centralized identification administration system
Anybody who has struggled to handle a number of identification techniques understands that it’s an costly and inefficient method. Authorities prospects who’ve adopted Microsoft Entra ID as their central company identification supplier (IdP) gained a holistic view of all customers and their entry permissions as required by the memo. In addition they gained a centralized entry coverage engine that mixes alerts from a number of sources, together with identities and gadgets, to detect anomalous person conduct, assess threat, and make real-time entry selections that adhere to Zero Belief rules.
Furthermore, Microsoft Entra ID allows single sign-on (SSO) to assets and apps, together with apps from Microsoft and 1000’s of different distributors, whether or not they’re on-premises or in Microsoft business or authorities clouds. When deployed because the central company IdP, Microsoft Entra ID additionally secures entry to assets in clouds from Amazon, Google, and Oracle.
Many authorities prospects are facilitating safe collaboration amongst totally different organizations by utilizing Microsoft Entra Exterior ID for business-to-business (B2B) collaboration to allow cross-cloud entry situations. They don’t have to present collaboration companions separate credentials for accessing functions and paperwork of their atmosphere, which reduces their cyberattack floor and spares their accomplice customers from sustaining a number of units of credentials for a number of identification techniques.
Utilizing Microsoft Entra ID to facilitate cross-organizational collaboration
Cross-tenant entry with Microsoft Entra Exterior ID
Certainly one of our authorities prospects, together with their accomplice company, configured cross-tenant entry settings to belief multifactor authentication claims from every person’s house tenant. Their accomplice company can now belief and implement robust phishing-resistant authentication for the client’s customers with out forcing them to check in a number of occasions to collaborate. The accomplice company additionally explicitly enforces, by way of a Conditional Entry authentication energy coverage, that the client’s customers should check in utilizing a private identification verification (PIV) card or a standard entry card (CAC) earlier than gaining entry.
Configure cross-tenant entry settings for B2B collaboration
One other authorities buyer wanted to present workers from totally different organizations throughout the identical company entry to shared companies functions comparable to human assets techniques. They used Microsoft Entra Exterior ID for B2B collaboration together with cross-cloud settings to allow seamless and safe collaboration and useful resource sharing for all company workers, different authorities companies (OGAs), and exterior companions. They used Microsoft Entra Conditional Entry coverage and cross-tenant entry settings to require that workers check in utilizing phishing-resistant authentication earlier than accessing shared assets. Belief relationships make sure that this method works whether or not the house tenant of an worker is in an Azure business or authorities cloud. In addition they enabled collaboration with companies that use an IdP apart from Microsoft Entra ID by establishing federation by way of the SAML 2.0 and WS-Fed protocols.
Subsequent step after standardizing on Microsoft Entra ID as your centralized IdP: Use Microsoft Entra ID Governance to automate lifecycle administration of visitor accounts in your tenant, so visitor customers solely get entry to the assets they want, for less than so long as they want it. Begin right here: What are lifecycle workflows?
Enabling robust multifactor authentication
Standardizing on Microsoft Entra ID has made it doable for our authorities prospects to allow phishing-resistant authentication strategies. Over the previous 18 months, we’ve labored with our US authorities prospects to extend adoption of phishing-resistant multifactor authentication with Microsoft Entra by nearly 2,000%.
From there, prospects configure Conditional Entry insurance policies that require robust phishing-resistant authentication for accessing functions and assets, as required by the memo. Utilizing Conditional Entry authentication energy, they’ll even set insurance policies to require extra, stronger authentication based mostly on the sensitivity of the appliance or useful resource the person is making an attempt to entry, or the operation they’re making an attempt to carry out.
Microsoft Entra helps robust phishing-resistant types of authentication:
- Certificates-based authentication (CBA) utilizing Private Identification Playing cards (PIV) or Frequent Entry Playing cards (CAC)
- System-bound passkeys
- FIDO2 safety keys
- Passkeys within the Microsoft Authenticator app
- Home windows Good day for Enterprise
- Platform single sign-on SSO for macOS gadgets (in preview)
For a deep dive into phishing resistant authentication in Microsoft Entra, discover the video collection Phishing-resistant authentication in Microsoft Entra ID.
Whereas Microsoft Entra ID can forestall the usage of widespread passwords, determine compromised passwords, and allow self-service password reset, a lot of our authorities prospects desire to require essentially the most safe types of authentication, comparable to sensible playing cards with x.509 certificates and passkeys, which don’t contain passwords in any respect. This makes signing in safer, simplifies the person expertise, and reduces administration complexity.
Implementing phishing-resistant multifactor authentication strategies with Microsoft Entra ID
Migrate to cloud authentication utilizing Staged Rollout
To cut back the associated fee and complexity of sustaining an on-premises authentication infrastructure utilizing Lively Listing Federation Companies (AD FS) for worker PIV playing cards, one company wished to make use of certificate-based authentication (CBA) in Microsoft Entra ID. To make sure the transition went easily, they moved customers with Staged Rollout, rigorously monitoring menace exercise utilizing Microsoft Entra ID Safety dashboards and Microsoft Graph API logs exported to their safety data and occasion administration (SIEM) system. They migrated all their customers to cloud-based CBA in Microsoft Entra in lower than three months and after monitoring the atmosphere for a time, confidently decommissioned their AD FS servers.
Public preview: Microsoft Entra ID FIDO2 provisioning APIs
An area authorities division selected an opt-in method for shifting workers and distributors to phishing-resistant authentication. Each person contacting the assistance desk for a password reset as a substitute acquired assist onboarding to Home windows Good day for Enterprise. This company additionally gave FIDO2 keys to all admins and set a Conditional Entry authentication energy coverage requiring all distributors to carry out phishing-resistant authentication. Their subsequent step might be to roll out device-bound passkeys managed within the Microsoft Authenticator app and implement their use by way of Conditional Entry. This can save them the expense of issuing separate bodily keys and provides their customers the acquainted expertise of authenticating securely from their cell system.
Supported identities and authentication strategies in Azure Digital Desktop
By giving customers entry to functions and assets by way of Azure Digital Desktop, one other giant company avoids the overhead of sustaining and supporting particular person gadgets and the software program operating on them. In addition they shield their atmosphere from doubtlessly unhealthy, misconfigured, or stolen gadgets. Whether or not workers use gadgets operating Home windows, MacOS, iOS, or Android, they run the identical Digital Desktop picture and check in, as coverage requires, utilizing phishing-resistant, passwordless authentication.
Subsequent step after enabling robust multifactor authentication: Configure Conditional Entry authentication energy to implement phishing-resistant authentication for accessing delicate assets. Begin right here: Overview of Microsoft Entra authentication energy.
Utilizing Conditional Entry insurance policies to authorize entry to assets
Utilizing Conditional Entry, our authorities prospects have configured fine-tuned entry insurance policies that take into account contextual details about the person, their system, their location, and real-time threat ranges to regulate which apps and assets customers can entry and below what circumstances.
To fulfill the memo’s third identification requirement, these prospects embrace device-based alerts in insurance policies that make authorization selections. For instance, Microsoft Entra ID Safety can detect whether or not a tool’s originating community is protected or unsafe based mostly on its geographic location, IP tackle vary, or whether or not it’s coming from an nameless IP tackle (for instance, TOR). Conditional Entry can consider alerts from Microsoft Intune or different cell system administration techniques to find out whether or not a tool is correctly managed and compliant earlier than granting entry. It will probably additionally take into account system menace alerts from Microsoft Defender for Endpoint.
Enabling Microsoft Entra Conditional Entry risk-based insurance policies
One authorities division enabled risk-based Conditional Entry insurance policies throughout their functions, requiring extra stringent sign-in strategies relying on ranges of person and sign-in threat. For instance, a person evaluated as ‘no-risk’ should at all times carry out multifactor authentication, a person evaluated as ‘low-medium threat’ should check in utilizing phishing-resistant multifactor authentication, and a person deemed ‘high-risk’ should check in utilizing a particular certificates issued to them by the division. The client has additionally configured coverage to require compliant gadgets, allow token safety, and outline sign-in frequency. To facilitate menace looking and automated mitigation, they ship their sign-in and different Microsoft Entra logs to Microsoft Sentinel.
Subsequent step after configuring primary Conditional Entry insurance policies: Configure risk-based Conditional Entry insurance policies utilizing Microsoft Intune. Begin right here: Configure and allow threat insurance policies.
Subsequent steps
On July 10, 2024, the White Home issued Memorandum M-21-14, “Administration Cybersecurity Priorities for the FY 2026 Price range.” One funds precedence calls on companies to transition towards absolutely mature Zero Belief architectures by September 30, 2026. Companies have to submit an up to date implementation plan to the Workplace of Administration and Price range inside 120 days of the memo’s launch. Companies within the Division of Protection should additionally implement Zero Belief by September 30, 2026, a yr sooner than the beforehand printed timeline.
Microsoft is right here that will help you rearchitect your atmosphere and implement your Zero Belief technique, so you may adjust to each milestone of the Govt Order. We’ve printed technical steerage and detailed documentation to assist federal companies use Microsoft Entra ID to satisfy identification necessities. We’ve additionally printed detailed steerage on assembly the Division of Protection Zero Belief necessities with Microsoft Entra ID.
Within the coming weeks and months, you’ll see bulletins about extra steps we’re taking to simplify your Zero Belief implementation, comparable to the overall availability of assist for device-bound passkeys in Microsoft Authenticator and Microsoft-managed Conditional Entry insurance policies that allow multifactor authentication by default for US authorities prospects.
We stay up for supporting you thru the following phases of your Zero Belief journey.
- Standardize on Microsoft Entra ID as your centralized identification supplier to safe each identification and to safe entry to your apps and assets. Begin right here: What’s Microsoft Entra ID?
- To facilitate safe cross-organization collaboration, configure cross-tenant entry settings and Conditional Entry insurance policies to require that companions accessing your assets check in utilizing phishing-resistant authentication. Begin right here: Microsoft Entra B2B in authorities and nationwide clouds.
- If you happen to’re utilizing CBA on AD FS, migrate to cloud-based CBA utilizing Staged Rollout and retire your on-premises federation servers. Begin right here: Migrate from AD FS Certificates-based Authentication (CBA) to Microsoft Entra ID CBA.
- Get rid of passwords altogether by enabling passwordless phishing-resistant authentication utilizing CBA, Home windows Good day for Enterprise, device-bound passkeys (FIDO2 safety keys or passkeys managed within the Microsoft Authenticator app), or Platform SSO for MacOS. Begin right here: Plan a passwordless authentication deployment in Microsoft Entra ID.
- Implement risk-based Conditional Entry insurance policies to regulate entry necessities dynamically. Begin right here: DoD Zero Belief Technique for the person pillar.
To be taught extra about Microsoft Safety options, go to our web site. Bookmark the Safety weblog to maintain up with our knowledgeable protection on safety issues. Additionally, comply with us on LinkedIn (Microsoft Safety) and X (@MSFTSecurity) for the most recent information and updates on cybersecurity.