In 2022 and 2023, Sophos X-Ops printed analysis about a toolset to sabotage the features of endpoint safety software program that was being developed and used at the side of a number of main ransomware gangs. Mandiant had beforehand named this device Poortry, and its loader software Stonestop.
The creators of the Poortry device had managed to get purpose-built, customized kernel-level drivers signed via Microsoft’s attestation signing course of. After we printed our analysis — and Microsoft closed the loophole that allowed these drivers to be signed — the device’s creators didn’t simply cease. They’ve continued so as to add options and performance to the Poortry driver, in an ongoing try and evade detection and to search out new methods to disable EDR and endpoint safety software program.
To elucidate the brand new options in Poortry, let’s evaluation how drivers work together with the working system, and the way the builders of this EDR killer developed their device over time.
How Home windows drivers can sabotage safety
Most EDR killers depend on a tool driver being loaded into the working system’s kernel, which supplies them entry to the sorts of low-level performance to have the ability to unhook and terminate numerous sorts of safety software program.
Below Home windows, which helps a large number of peripherals and related parts, kernel-mode drivers are given broad latitude to those sorts of low-level features. Below regular circumstances, these drivers don’t work together with software program or {hardware} from different firms or producers, however there isn’t a enforcement of this conduct. Thus, if a signed reliable driver doesn’t correctly validate the processes interacting with it, EDR killers can exploit a few of its options to take away protecting measures.
Microsoft has developed a wide range of ways in which their working techniques can management whether or not drivers get loaded in any respect, such because the Driver Signature Enforcement mechanism: Drivers have to be digitally signed by a software program writer Microsoft trusts earlier than they’ll load.
The builders of EDR killers exploit the gaps on this belief mannequin: They could use a driver susceptible to abuse that was as soon as printed by a reliable software program firm; In addition they may signal their very own driver with a reliable code-signing certificates (and there are numerous methods to acquire stolen or leaked certificates).
Normally there are 3 ways EDR killer builders abuse code signatures:
Abuse of leaked certificates
That is essentially the most simple approach to deal with the issue: Discover a leaked, stolen, or in any other case compromised code-signing certificates from a reliable firm, and use it to signal your driver (or to trick Root Certificates Authorities into issuing a certificates to you).
For all variations of Home windows that got here after Home windows 10 model 1607, Microsoft has required all third-party builders of kernel-mode drivers to submit their driver to Microsoft’s developer portal, to be cross-signed by Microsoft. Nonetheless, cross-signed drivers not signed by Microsoft are nonetheless allowed to be loaded if it fulfills one of many following :
- The PC was upgraded from an earlier launch of Home windows to Home windows 10, model 1607
- Safe Boot is switched off within the system BIOS
- Driver was signed with an end-entity certificates issued previous to July 29, 2015 that chains to a supported cross-signed CA
Though the replace lowered the hazard of cross-signed drivers that had been signed by stolen certificates, the third bullet creates a loophole that permits the second methodology for attackers.
Signature timestamp forgery
With the intention to keep compatibility with older drivers, Home windows hundreds drivers signed with “an end-entity certificates issued previous to July 29, 2015 that chains to a supported cross-signed CA.”
When signing a kernel driver, Microsoft gives the software program writer with a device named signtool.exe. Along with signing the supplied file, signtool additionally checks to make sure that the supplied certificates remains to be legitimate. A technique to make sure that is to make use of the perform
By way of a sequence of hooks to those low-level API calls contained in the working system, attackers can alter the signing course of and bypass these checks to signal their very own kernel driver. One of many features being hooked on this approach is GetLocalTime to return a cast timestamp to cross via the checks in signtool.exe.
Bypassing Microsoft attestation signing
The ultimate methodology is to get via Microsoft’s attestation signing course of, and get the kernel driver signed straight by Microsoft. That is in all probability essentially the most troublesome to realize, but in addition gives a signature a robust WHQL certificates that was issued by Microsoft itself – virtually a holy grail of digital signatures.
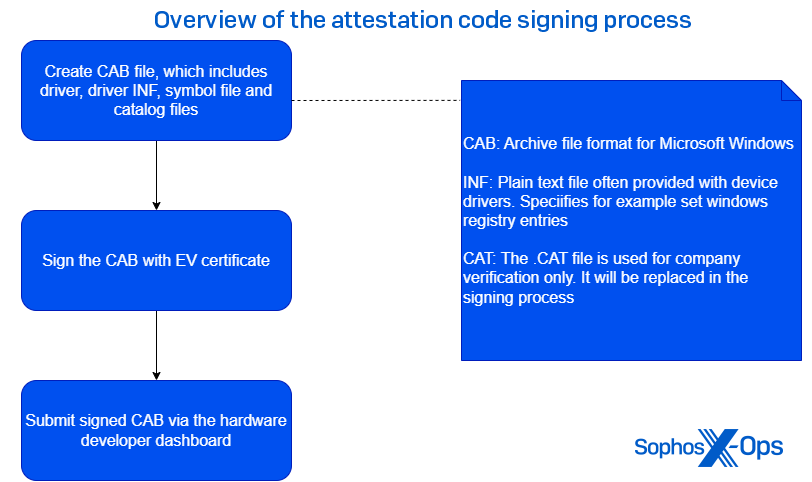
To abuse this methodology, attackers want:
- A legitimate EV certificates
- Entry to the Microsoft developer portal
If these necessities are fulfilled, they’ll put together a CAB file, which incorporates the driving force itself, signal it with the EV certificates, and submit it to the dashboard.
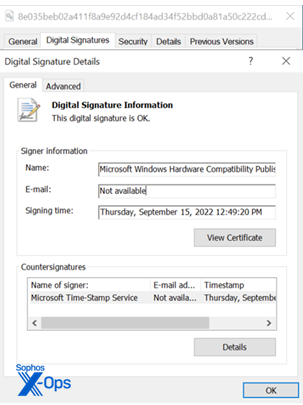
As soon as submitted, the driving force undergoes a number of checks to make sure that the driving force is just not malicious. If the driving force passes these assessments, it is going to carry the “Microsoft Home windows {Hardware} Compatibility Writer” signature.
Poortry & Stonestop: A Related Risk Since 2022
Poortry (additionally typically known as BurntCigar) is a malicious kernel driver used at the side of a loader named Stonestop by Mandiant, who first reported on the device’s existence. The motive force bypasses Driver Signature Enforcement by utilizing any of the three methods described above. Each are closely obfuscated by industrial or open-source packers, akin to VMProtect, Themida or ASMGuard.
From the top of 2022 to mid-2023, Poortry variants carried the Microsoft WHQL certificates. Nonetheless, on account of joint work Between Sophos X-Ops and Microsoft, most of this attestation signed samples have been discovered and Microsoft deactivated the accounts that have been abused to get these drivers signed.
Poortry’s creators weren’t deterred; As a substitute, they switched to both Signature Timestamp Forging or acquiring a legitimate leaked certificates.
During the last 12 months, we have been in a position to hyperlink the usage of Poortry to assaults involving not less than 5 main ransomware households:
- CUBA
- BlackCat
- Medusa
- LockBit
- RansomHub
Since 2023, we’ve noticed risk actors repeatedly use Poortry throughout assaults. One attribute we noticed in our earlier analysis is that Poortry’s creators change their packer ceaselessly, making a quantity of barely modified variants based mostly off the unique. In our analysis, we discovered a number of completely different WHQL-signed variants, full of completely different industrial or non-commercial packers.
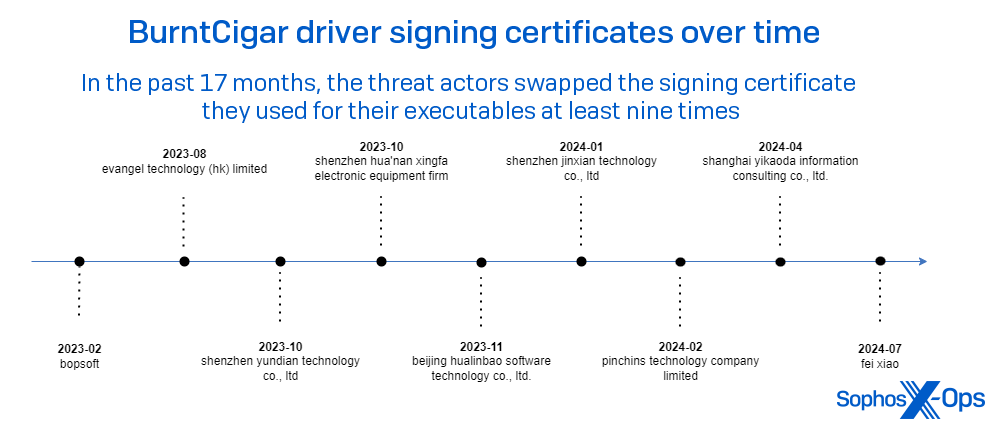
Since that venue was closed to them, Poortry’s makers now deploy the drivers signed by all kinds of non-Microsoft certificates.
The determine beneath illustrates a timeline of the noticed signer names utilized by Poortry’s payload driver over a 15 month interval.
It’s worthwhile mentioning that typically we make our observations throughout incident response engagements, and at different occasions collected as telemetry. One factor we will be certain of is that the full quantity and number of certificates is bigger than our commentary alone can decide.
Enjoying certificates roulette
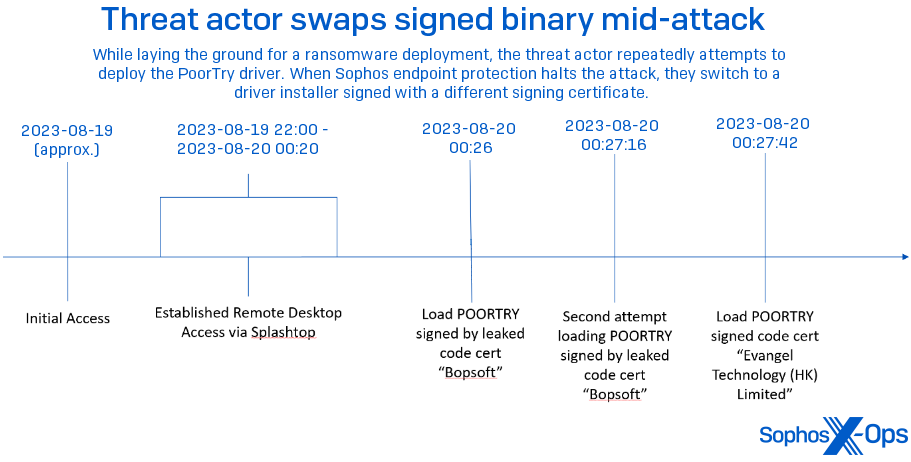
Sophos, sometimes, has noticed a risk actor deploy variants of Poortry on completely different machines inside a single property throughout an assault. These variants include the identical payload, however signed with a distinct certificates than the driving force first seen used throughout the assault.In August 2023, throughout a Sophos X-Ops investigation, we discovered that attackers gained preliminary entry through a distant entry device named SplashTop. As quickly because the attackers have been on the community, they deployed Poortry and Stonestop. However the signer identify, “bopsoft,” was already generally known as a stolen certificates, and was blocked utilizing a behavioral rule.
Inside 30 seconds after the final try utilizing the “Bopsoft” signed code, the attackers have been loading a distinct Poortry driver, this one signed by “Evangel Know-how (HK) Restricted.” The host was rapidly remoted and the assault thwarted.
Transition from EDR killer To EDR wiper
In July 2024, whereas engaged in an incident the place adversaries tried to deploy RansomHub ransomware, Sophos CryptoGuard thwarted the tried knowledge encryption as analysts closed off the attackers’ factors of entry. A post-incident evaluation revealed that two further executables had been dropped on a number of machines previous to the ultimate ransomware assault:
<d>Customers<u>desktopc7iy3d.exe <d>Customers<u>appdatalocaltempusnnr.sys
By way of a mix of static and dynamic evaluation, we decided the recordsdata to be Poortry and Stonestop. Among the many variations we noticed between the prior model and this model, Poortry now may also delete vital EDR parts fully, as an alternative of merely terminating their processes.
Development Micro reported in 2023 that Poortry had developed the potential to delete recordsdata off disk, however this was the primary time we noticed this characteristic utilized in an assault.
A more in-depth take a look at the most recent variants
Each the Stonestop executable and the Poortry driver are closely packed and obfuscated. This loader was obfuscated by a closed-source packer named ASMGuard, accessible on Github.
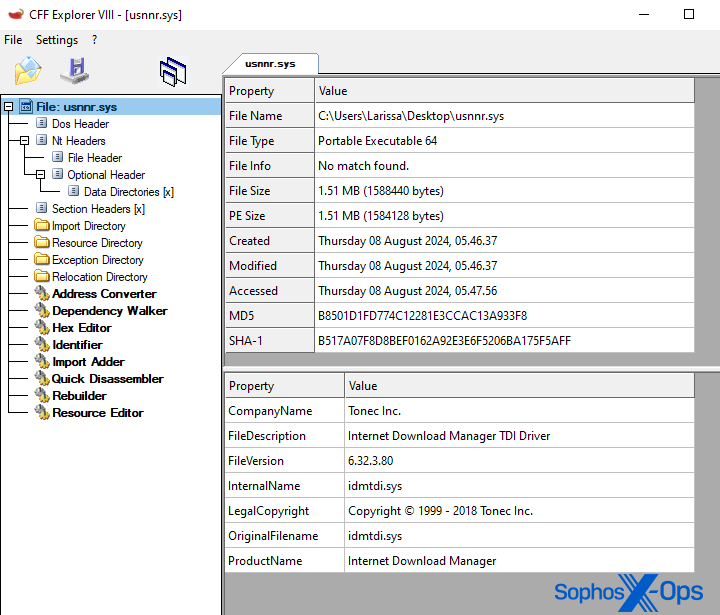
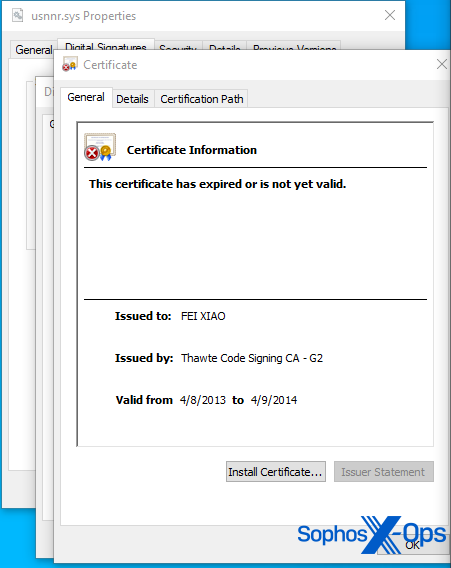
The motive force is signed with a certificates carrying the signer identify “FEI XIAO.” Sophos X-Ops has excessive confidence the signature timestamp was cast to signal the driving force. Notably, it tries to masquerade by utilizing the identical data in its properties sheet as a driver (idmtdi.sys) for a commercially accessible software program, Web Obtain Supervisor by Tonec Inc. Nevertheless it isn’t this software program bundle’s driver – the attackers merely cloned the knowledge from it.
For explanatory functions, we divide the execution circulation into three distinct phases.
Initialization Part
In incidents we’ve tracked, risk actors drop Poortry and Stonestop collectively, into the identical listing. On execution, Stonestop checks for the corresponding driver within the present listing.
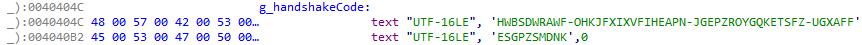
The filename and gadget identify of the driving force are each hardcoded into the loader. Upon begin, the loader fetches the deal with of the malicious kernel driver and initiates a handshake by sending a hardcoded string to the driving force through the DeviceIoControl API name.
General, communication between the parts occurs via this DeviceIoControl API. Every characteristic supplied by the kernel-mode element is triggered through sending a distinct IOCTL code. Earlier variants communicated through the IRP_MJ_DEVICE_CONTROL handler. The present variant makes use of the IRP_MJ_MAXIMUM_FUNCTION handler now to obtain I/O request packets.
It’s worthwhile mentioning that the mappings from IOCTL code to characteristic has modified since our final evaluation. For instance, the command to kill a particular course of by course of ID was triggered by sending an I/O request packet with code 0x222094. The newest pattern maps the IOCTL code 0x222144 to the identical performance.
Since Development Micro’s 2023 report, Poortry’s builders elevated the variety of receivable IOCTL codes from 10 to 22. Our evaluation of all accessible options remains to be ongoing.
Like earlier variations, a handshake is initiated by sending a hardcoded string to the driving force. As soon as the handshake worth is accepted, it units a flag within the binary that permits the functionalities of the malicious driver.
Impairment Part
The second part is concentrated on disabling EDR merchandise via a sequence of various methods, akin to removing or modification of kernel notify routines.
Safety drivers make use of a number of completely different options supplied by the Home windows OS to register callbacks when particular occasions on the Home windows system happen. An instance can be the perform PsSetCreateProcessNotifyRoutine, which provides a driver provided callback routine when a brand new course of is created.
Eliminating these callback routines are sometimes a vital step to render EDR merchandise ineffective. In 2022, we additionally wrote a few related case the place BlackByte ransomware abused a reliable susceptible driver to take away vital kernel notify routines.
Within the second part, we noticed a complete of seven distinct IOCTL codes are despatched to the kernel-mode element. Solely the performance mapped to 0x222400 is executed. The opposite options bailed out early on account of particular flags being set within the binary. We suspect that the non-triggered functionalities are both experimental, solely triggered on particular kind of techniques, or just disabled.
The IOCTL codes and their mapped behaviors are as follows:
0x2220C0 (Disabled)
When obtained, Poortry enters an extra initialization routine, fetching addresses of assorted vital buildings and features.
0x222100 (Disabled)
When obtained, Poortry makes an attempt to disable or allow kernel callbacks through modification of the PspNotifyEnableMask flag. It is a widespread trick utilized by rootkits to allow or disable kernel routine callbacks, as defined by this text.
0x222104 (Disabled)
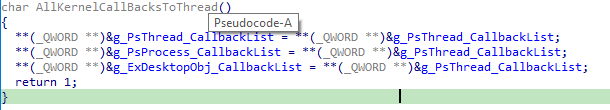
When it receives this IOCTL code, Poortry modifies the kernel callbacks of the PsProcess, PsThread and ExDesktopObj object sorts. These are kernel-mode knowledge buildings that symbolize particular objects within the Home windows kernel. Self-explanatory, the PsProcess object kind represents a course of object. These object sorts additionally include a variable pointing to the callbacks registered for the corresponding object.
As a result of this characteristic was disabled, we’re uncertain how adversaries may goal to switch these callback lists. One potential situations is perhaps to both disable them totally by setting the callbacks to a customized perform with none performance, merely returning immediately,
0x222108 (Disabled)
When obtained, Poortry modifies the CmpCallbackCount variable to both allow or disable registry kernel callbacks. The variable is used to rely the variety of registered callbacks. We suspect that if this worth is patched to zero, the callbacks might be rendered ineffective.
0x22210C (Disabled)
When obtained, Poortry makes an attempt to take away the fltMgr.sys driver from the FileSystemFastFat and FileSystemNtfs gadget by use of the DeviceIoDetachDevice perform. The perform is normally utilized by legitimate drivers to scrub up throughout shutdown. Nonetheless, rootkits can use the perform to forestall focused drivers from receiving any additional I/O requests.
fltMgr.sys is the filter supervisor on Home windows. This driver is used to increase or modify the performance of present functionalities on the Home windows system. The motive force can also be typically utilized by EDR merchandise.
We suspect by detaching it through use of IoDetachDevice put in filters are rendered ineffective on the focused system.
0x2221C0 (Disabled)
When obtained, Poortry enters routines to fetch the tackle of main features handlers of ClassPnp.sys and ntfs.sys, akin to NtfsFsdClose or NtfsFsdRead of ntfs.sys. Thus, we suspect that this routine can be utilized as an extra initialization routine to fetch vital perform addresses which are utilized by different options.
0x222400 (Enabled)
When obtained, Poortry disables put in kernel callbacks via a sequence of various methods. The user-mode element consists of the identify of the focused driver when the I/O request packet is distributed.
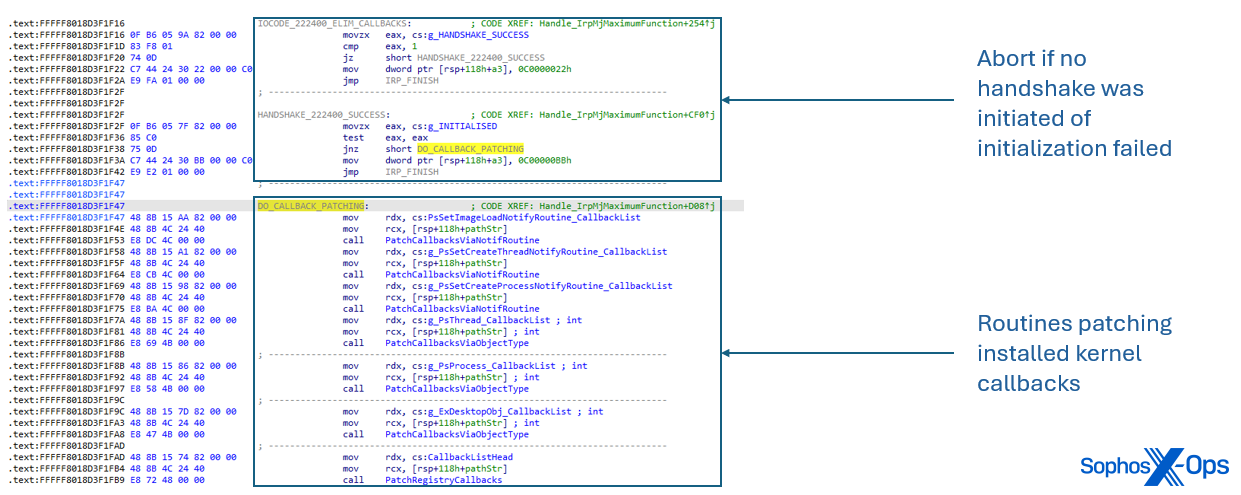
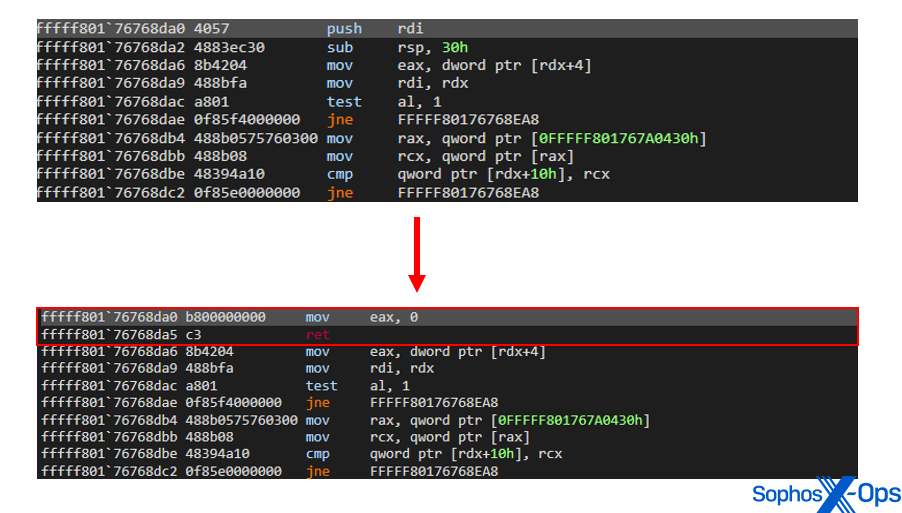
Kernel callbacks put in through PsSetLoadImageNotifyRoutine, PsSetCreateThreadNotifyRoutine and PsSetCreateProcessNotifyRoutine are patched. On the prologue of the callback perform, Poortry modifies the primary instruction to immediately return zero when entered.
Thus far, we recognized the next methods to render kernel callbacks and safety drivers ineffective:
- Inside buildings utilized by the corresponding features PsSetLoadImageNotifyRoutine, PsSetCreateThreadNotifyRoutine and PsSetCreateProcessNotifyRoutine are iterated. If the callback belongs to a tagged safety driver, As a consequence, the registered callback perform are exiting instantly with out executing any of its meant operations.
- The Home windows kernel implements essential knowledge buildings akin to PsProcess, PsThread and ExDesktopObject that symbolize basic components of the Home windows working system. These construction include a variable named CallbackList that manages all callback routines related to the precise object. Poortry iterates this checklist and if the callback belongs to a tagged safety driver, As a consequence, the registered callback perform are exiting instantly with out executing any of its meant operations.
- An inner linked listed utilized by CmRegisterCallback and CmUnregisterCallback is iterated. This linked checklist accommodates perform factors to registered registry and object callbacks. If the callback belongs to a tagged safety driver, the prologue of the perform is patched.
- Poortry makes use of the exported perform FltEnumerateFilters from fltMgr.sys to iterate via utilized filters. If the filter belongs to a tagged safety driver, the prologue of the perform is patched.
- Whereas we weren’t in a position to straight set off the performance, we now have discovered proof that Poortry can abuse the IoDetachDevice perform to detach a tool object from a system’s gadget stack. In opposite to the performance supplied by IOCTL code 0x22210C, it’s much less evasive and detaches gadgets provided that the gadget identify matches the enter identify ship through DeviceIoControl.
Cleanup Part
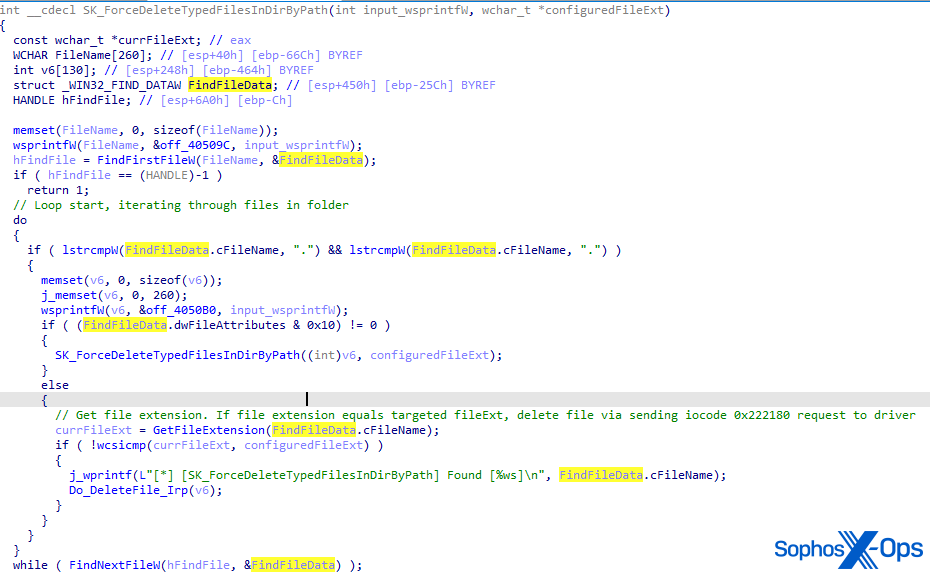
After impairment, the EDR killer goals at terminating security-related processes and rendering the EDR agent ineffective by wiping vital recordsdata off disk.
First, the user-mode element sends a number of I/O requests with IOCTL code 0x222144 to the kernel-mode element, together with the method id of the method to kill.
The loader accommodates an inventory of hardcoded paths pointing on the location the place EDR merchandise are put in. It iterates all sub-folders and recordsdata within the folder and deletes recordsdata vital to the EDR agent, akin to EXE recordsdata or DLL recordsdata by sending an IOCTL request with code 0x222180 to the driving force. The despatched request consists of the trail of the file to delete.
Notably, the user-mode element can function in two modes:
- Deleting recordsdata by kind
- Deleting recordsdata by identify
We suspect that the writer added these operation modes to make sure flexibility when aiming for various targets. We additionally imagine that the checklist of hardcoded paths pointing at set up folders of EDR merchandise change relying on the goal.
In conclusion
Poortry, and its related loader Stonestop, have undergone a critical characteristic enhancement within the 20 months since Sophos and Microsoft launched a joint report on the EDR killer’s abuse of the WHQL signing mechanism. What was as soon as a comparatively easy device for unhooking “troublesome” endpoint safety parts has turn into, in and of itself, a Swiss Military Knife of malicious capabilities abusing a nearly limitless provide of stolen or improperly used code signing certificates with the intention to bypass Driver Signature Verification protections.
Poortry’s builders made it a differentiating attribute of their device that it may do extra than simply unhook an EDR or endpoint safety anti-tamper driver. Poortry has developed into one thing akin to a rootkit that additionally has with finite controls over numerous completely different API calls used to regulate low-level working system performance. It additionally now has the capability to wipe its enemies – safety software program – proper off the disk as a approach to clear the trail for a ransomware deployment.
Sophos X-Ops has printed Indicators of Compromise (IOCs) to our GitHub.