
A wave of assaults that began in July 2024 depend on a much less widespread method referred to as AppDomain Supervisor Injection, which might weaponize any Microsoft .NET software on Home windows.
The method has been round since 2017, and a number of proof-of-concept apps have been launched over time. Nonetheless, it’s sometimes utilized in purple staff engagements and seldomly noticed in malicious assaults, with defenders not actively monitoring it.
The Japanese division of NTT has tracked assaults that finish with deploying a CobaltStrike beacon that focused authorities companies in Taiwan, the navy within the Philippines, and power organizations in Vietnam.
Ways, strategies, and procedures, and infrastructural overlaps with current AhnLab studies and different sources, recommend that the Chinese language state-sponsored risk group APT 41 is behind the assaults, though this attribution has low confidence.
AppDomain Supervisor Injection
Much like normal DLL side-loading, AppDomainManager Injection additionally entails using DLL information to realize malicious objectives on breached programs.
Nonetheless, AppDomainManager Injection leverages .NET Framework’s AppDomainManager class to inject and execute malicious code, making it stealthier and extra versatile.
The attacker prepares a malicious DLL that incorporates a category inheriting from the AppDomainManager class and a configuration file (exe.config) that redirects the loading of a authentic meeting to the malicious DLL.
The attacker solely wants to position the malicious DLL and config file in the identical listing because the goal executable, with no need to match the identify of an current DLL, like in DLL side-loading.
When the .NET software runs, the malicious DLL is loaded, and its code is executed throughout the context of the authentic software.
Not like DLL side-loading, which could be extra simply detected by safety software program, AppDomainManager injection is tougher to detect as a result of the malicious habits seems to come back from a authentic, signed executable file.
GrimResource assaults
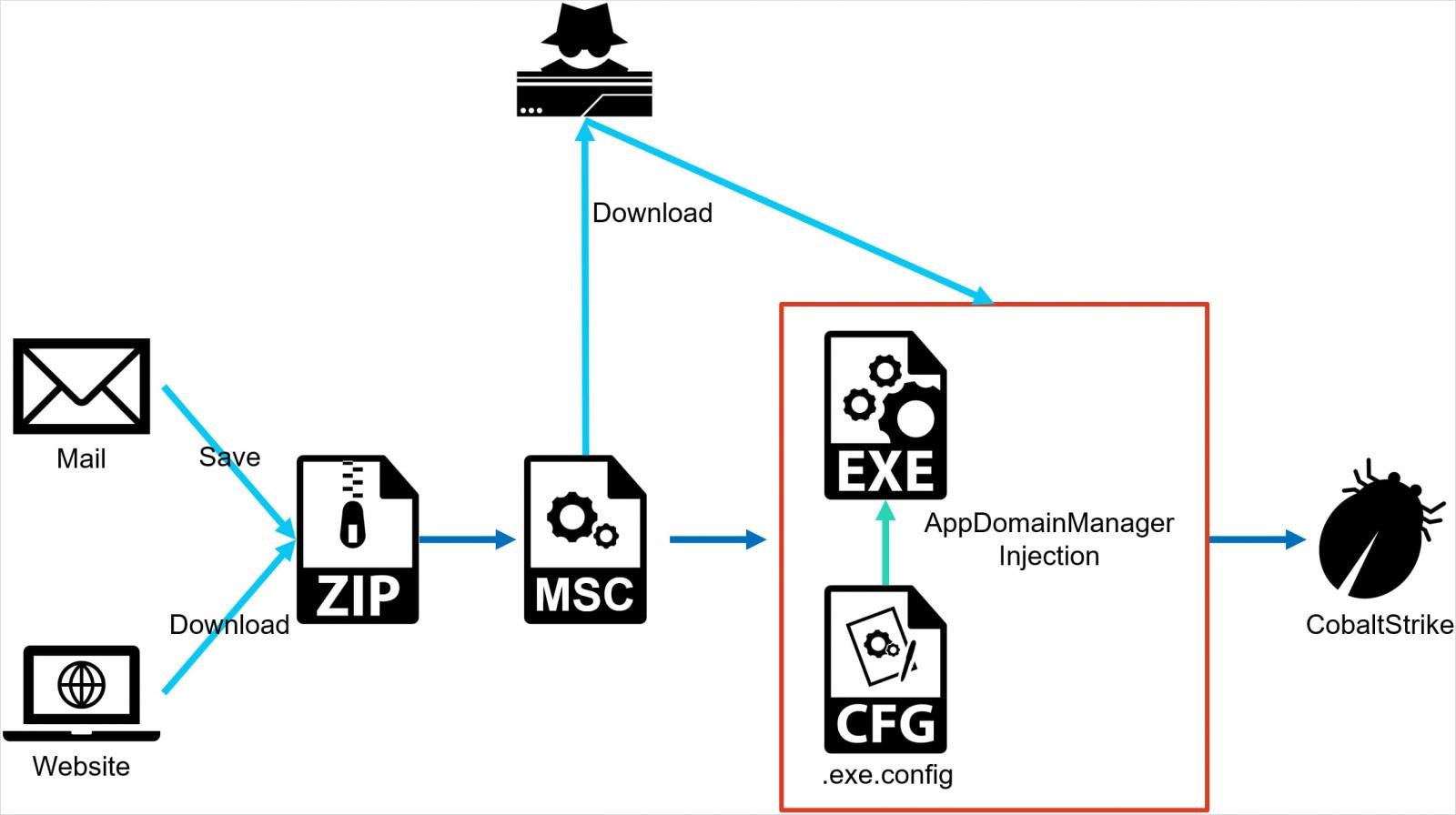
The assaults NTT noticed begin with the supply of a ZIP archive to the goal that incorporates a malicious MSC (Microsoft Script Part) file.
When the goal opens the file, malicious code is executed instantly with out additional person interplay or clicks, utilizing a way referred to as GrimResource, described intimately by Elastic’s safety staff in June.
GrimResource is a novel assault method that exploits a cross-site scripting (XSS) vulnerability within the apds.dll library of Home windows to execute arbitrary code by Microsoft Administration Console (MMC) utilizing specifically crafted MSC information.
The method permits attackers to execute malicious JavaScript, which in flip can run .NET code utilizing the DotNetToJScript methodology.
The MSC file within the newest assaults seen by NTT creates an exe.config file in the identical listing as a authentic, signed Microsoft executable file (e.g. oncesvc.exe).
This configuration file redirects the loading of sure assemblies to a malicious DLL, which incorporates a category inheriting from the .NET Framework’s AppDomainManager class and is loaded as a substitute of the authentic meeting.
In the end, this DLL executes malicious code throughout the context of the authentic and signed Microsoft executable, utterly evading detection and bypassing safety measures.
Supply: NTT
The ultimate stage of the assault is loading a CobaltStrike beacon on the machine, which the attacker might use to carry out a broad vary of malicious actions, together with introducing further payloads and lateral motion.
Though it is not sure that APT41 is liable for the assaults, the mix of the AppDomainManager Injection and GrimResource strategies signifies that the attackers have the technical experience to combine novel and less-known strategies in sensible instances.